In today's interconnected world, IoT device remote SSH example has become a critical topic for both hobbyists and professionals alike. As more devices get connected to the internet, understanding how to securely access and manage these devices remotely is essential. Secure Shell (SSH) provides a robust solution for remote access, ensuring data integrity and confidentiality. Whether you're a beginner or an advanced user, this guide will walk you through everything you need to know about IoT device remote SSH examples.
IoT (Internet of Things) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices have become integral to modern life. However, with great power comes great responsibility. Ensuring secure communication between devices is paramount, and SSH plays a pivotal role in achieving this.
This article aims to provide a detailed exploration of IoT device remote SSH examples. By the end, you'll have a comprehensive understanding of how SSH works, its implementation, and practical use cases. Let's dive in!
Read also:Movierulz Download 2023
Table of Contents
- Introduction to SSH
- IoT Remote SSH Basics
- Why Use SSH for IoT Devices?
- Setting Up SSH on IoT Devices
- Remote SSH Examples
- Security Best Practices
- Troubleshooting Common Issues
- Advanced SSH Techniques
- IoT Remote SSH Use Cases
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol designed for secure communication over unsecured networks. It provides a secure channel for data exchange between a client and a server, ensuring confidentiality, integrity, and authentication. SSH is widely used for remote administration, file transfers, and tunneling.
SSH operates on a client-server model, where the client initiates a connection to the server. The server authenticates the client using public key cryptography or password-based authentication. Once authenticated, a secure session is established, enabling the client to execute commands on the server.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between the client and server, preventing eavesdropping.
- Authentication: SSH supports multiple authentication methods, including public key, password, and certificate-based authentication.
- Port Forwarding: SSH allows for secure tunneling of other protocols, such as HTTP or FTP.
IoT Remote SSH Basics
When it comes to IoT devices, remote access is often necessary for monitoring, configuration, and troubleshooting. IoT device remote SSH example demonstrates how SSH can be used to securely connect to these devices from anywhere in the world. This section covers the fundamental concepts of using SSH with IoT devices.
Why IoT Devices Need Remote Access
- Monitoring: IoT devices often require real-time monitoring to ensure optimal performance.
- Configuration: Remote access allows administrators to configure devices without physical presence.
- Troubleshooting: Diagnosing and resolving issues remotely saves time and resources.
Why Use SSH for IoT Devices?
SSH offers several advantages when used with IoT devices, making it a preferred choice for secure remote access. Here are some compelling reasons:
- Security: SSH encrypts all communications, protecting sensitive data from unauthorized access.
- Reliability: SSH connections are stable and can be configured to withstand network interruptions.
- Compatibility: SSH is supported by a wide range of operating systems and devices, ensuring broad compatibility.
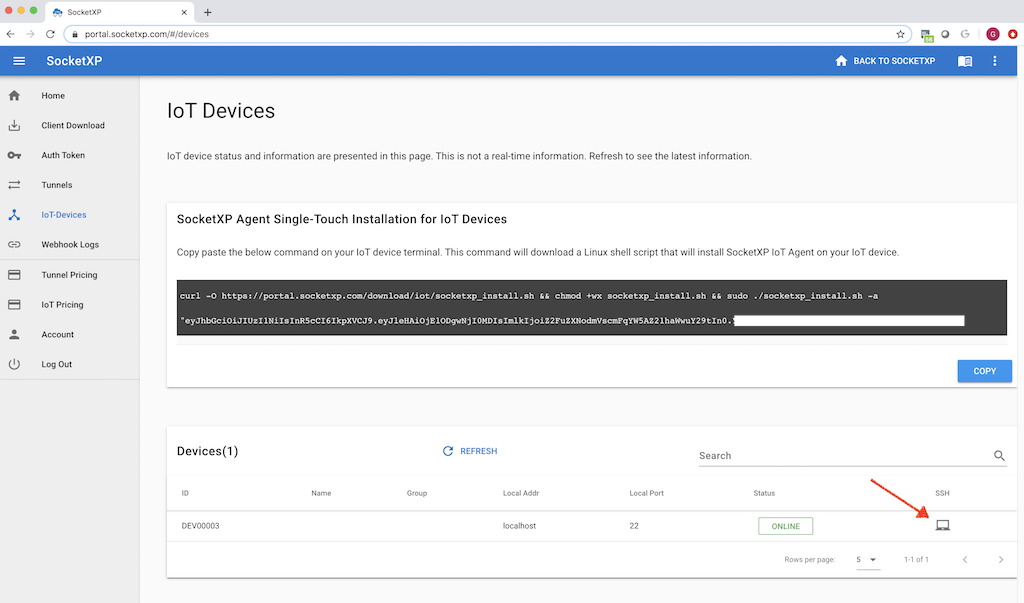
Setting Up SSH on IoT Devices
Configuring SSH on IoT devices involves several steps, including enabling the SSH service, generating keys, and setting up authentication. This section provides a step-by-step guide to setting up SSH on common IoT platforms.
Enabling SSH on Raspberry Pi
For Raspberry Pi users, enabling SSH is straightforward:
Read also:Moveirulz
- Insert the SD card into your computer.
- Create an empty file named "ssh" in the boot partition.
- Eject the SD card and insert it back into the Raspberry Pi.
Remote SSH Examples
Now that you have SSH configured on your IoT device, let's explore some practical examples of using SSH for remote access.
Example 1: Connecting to an IoT Device
To connect to an IoT device using SSH, open a terminal and use the following command:
ssh username@device_ip_address
Replace "username" with the appropriate username and "device_ip_address" with the IP address of your IoT device.
Example 2: Transferring Files
SSH can also be used to transfer files between your local machine and IoT device using the Secure Copy Protocol (SCP):
scp local_file_path username@device_ip_address:remote_file_path
Security Best Practices
While SSH provides a secure method for remote access, it's essential to follow best practices to minimize risks:
- Use Public Key Authentication: Disable password-based authentication and rely on public key cryptography for added security.
- Disable Root Login: Restrict direct root access to prevent unauthorized users from gaining administrative privileges.
- Regularly Update Software: Keep your SSH server and client software up to date to protect against vulnerabilities.
Troubleshooting Common Issues
Even with proper configuration, issues may arise when using SSH with IoT devices. Here are some common problems and their solutions:
Connection Timeout
If you encounter a connection timeout, ensure that:
- The device is connected to the network.
- Firewall rules allow SSH traffic on port 22.
- The SSH service is running on the device.
Advanced SSH Techniques
For advanced users, SSH offers several powerful features that can enhance productivity and security:
SSH Tunnels
SSH tunnels allow you to securely forward traffic from one network to another. This is particularly useful for accessing services behind firewalls or NATs.
SSH Key Management
Managing SSH keys effectively is crucial for maintaining security. Consider using tools like ssh-agent or ssh-add to streamline key management.
IoT Remote SSH Use Cases
IoT device remote SSH example extends beyond simple access scenarios. Here are some real-world use cases:
- Remote Monitoring: Use SSH to monitor sensor data in real-time.
- Automated Deployments: Automate software updates and deployments using SSH scripts.
- Secure Communication: Establish secure tunnels for communication between IoT devices.
Conclusion
In conclusion, mastering IoT device remote SSH example is essential for anyone working with IoT devices. SSH provides a secure, reliable, and versatile solution for remote access, enabling efficient management and monitoring of IoT devices. By following the best practices outlined in this guide, you can ensure the security and integrity of your IoT deployments.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, let's build a smarter, safer world!
Data Sources: SSH Official Documentation, Raspberry Pi SSH Guide, Microsoft OpenSSH Overview