IoT remote access SSH example is a powerful solution for managing and monitoring connected devices remotely. As the Internet of Things (IoT) continues to expand, secure access to devices becomes critical. Secure Shell (SSH) plays a pivotal role in facilitating this secure communication.
With IoT devices becoming more integrated into daily operations, businesses and individuals alike face challenges in ensuring secure access to these devices. SSH offers a robust framework that addresses these challenges by encrypting data transmissions and providing authentication mechanisms.
This article will delve into the intricacies of IoT remote access using SSH, complete with practical examples and expert insights. Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge to implement secure IoT connections effectively.
Read also:N
Table of Contents
- Introduction to SSH
- IoT Remote Access Overview
- Why SSH for IoT?
Basic SSH Setup
- Securing SSH Connections
IoT Remote Access SSH Example
- Best Practices for IoT SSH
- Troubleshooting SSH Connections
Alternative Protocols
- Future of IoT and SSH
- Conclusion
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol designed for secure data communication over unsecured networks. It ensures the integrity and confidentiality of data exchanged between devices by encrypting all transmissions. SSH is widely used for remote login and command execution but has become indispensable in IoT environments.
The protocol operates on a client-server model, where the client initiates a connection to the server. SSH uses public-key cryptography for authentication and symmetric encryption for data transfer, making it one of the most secure methods for remote access.
SSH has become a cornerstone for IoT remote access SSH example implementations, offering a reliable and secure way to manage IoT devices from anywhere in the world. Its adaptability and robust security features make it a preferred choice for developers and network administrators.
IoT Remote Access Overview
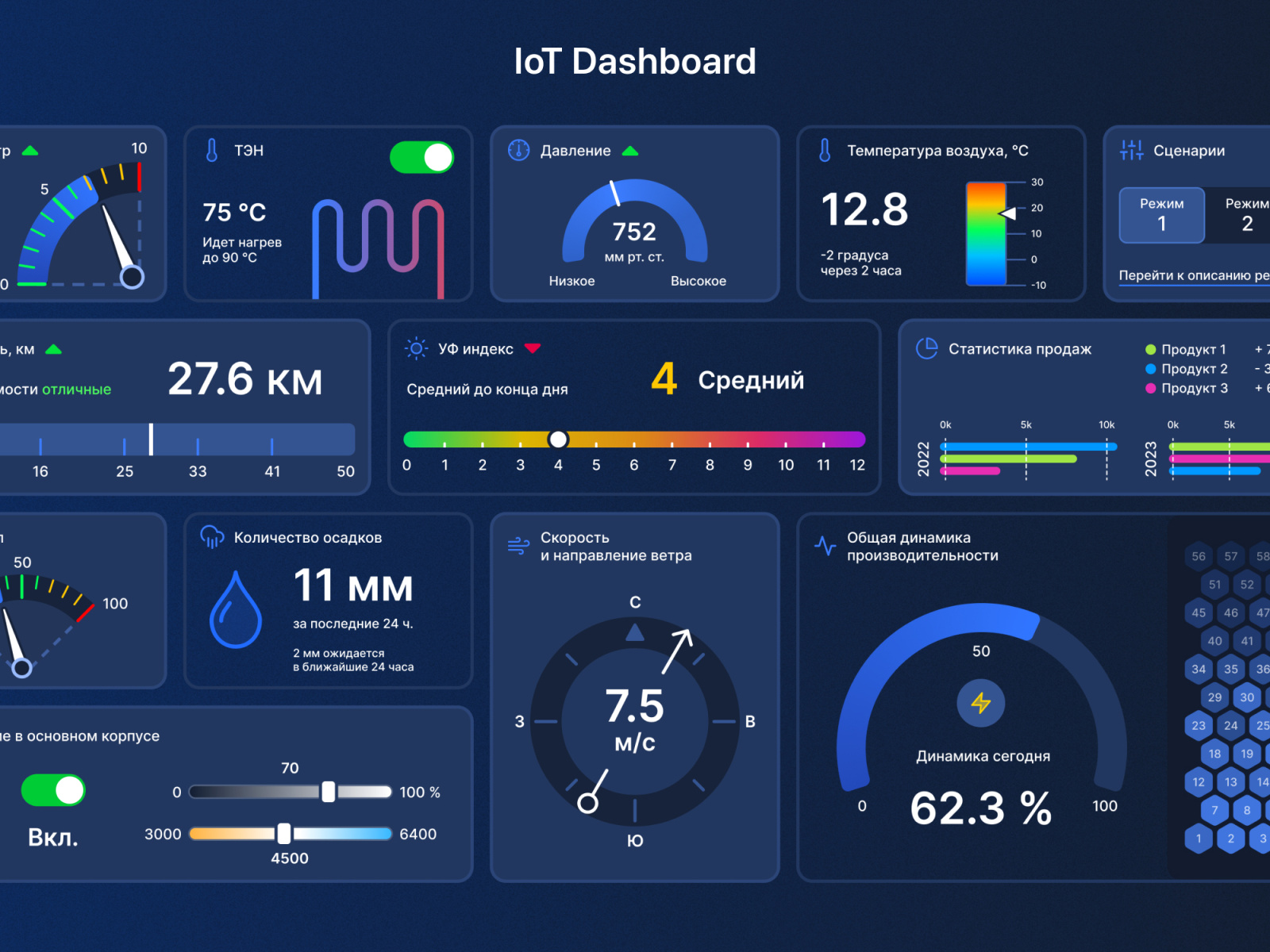
IoT remote access refers to the ability to control, monitor, and interact with IoT devices from a remote location. This capability is essential for maintaining and troubleshooting devices in real-time without physical presence. The proliferation of IoT devices across industries has increased the demand for secure and efficient remote access solutions.
Key benefits of IoT remote access include improved operational efficiency, reduced downtime, and enhanced scalability. However, the challenge lies in ensuring that these connections are secure and resistant to unauthorized access. This is where SSH comes into play, offering a secure channel for IoT remote access.
With the growing number of IoT devices, the importance of secure remote access cannot be overstated. Implementing SSH as part of an IoT infrastructure ensures that sensitive data remains protected while enabling seamless device management.
Read also:5movierulz 2024 Download In Telugu
Why SSH for IoT?
SSH is the preferred protocol for IoT remote access SSH example due to its strong security features and ease of implementation. It provides end-to-end encryption, ensuring that data transmitted between devices is secure from eavesdropping and tampering.
Key reasons for using SSH in IoT environments include:
- Encryption: SSH encrypts all data transmissions, safeguarding sensitive information.
- Authentication: It uses public-key cryptography for secure authentication, preventing unauthorized access.
- Reliability: SSH is a mature and stable protocol, making it a reliable choice for IoT applications.
- Compatibility: SSH works across various platforms and devices, ensuring seamless integration into existing systems.
These features make SSH an ideal choice for securing IoT remote access, protecting both the devices and the data they handle.
Basic SSH Setup
Setting up SSH for IoT remote access involves several steps, starting with the installation and configuration of the SSH server on the target device. Below is a step-by-step guide to help you get started:
- Install SSH Server: Begin by installing an SSH server on your IoT device. For Linux-based systems, you can use OpenSSH, which is widely supported and easy to configure.
- Configure SSH: Modify the SSH configuration file (usually located at /etc/ssh/sshd_config) to set up the desired parameters, such as port number and authentication methods.
- Enable Public-Key Authentication: Generate an SSH key pair on your client machine and copy the public key to the IoT device to enable passwordless authentication.
- Restart SSH Service: After making changes to the configuration, restart the SSH service to apply the new settings.
Once the basic setup is complete, you can test the connection to ensure that SSH is functioning correctly. This foundational setup is essential for implementing secure IoT remote access SSH example solutions.
Securing SSH Connections
Securing SSH connections is paramount, especially in IoT environments where devices often operate in untrusted networks. Below are some strategies to enhance the security of your SSH setup:
- Disable Password Authentication: Use public-key authentication instead of passwords to prevent brute-force attacks.
- Change Default Port: Modify the default SSH port (22) to a non-standard port to reduce the risk of automated attacks.
- Implement Firewall Rules: Restrict access to the SSH port by configuring firewall rules to allow connections only from trusted IP addresses.
- Use Strong Keys: Ensure that your SSH keys are sufficiently long and complex to resist cracking attempts.
By implementing these security measures, you can significantly reduce the risk of unauthorized access to your IoT devices through SSH.
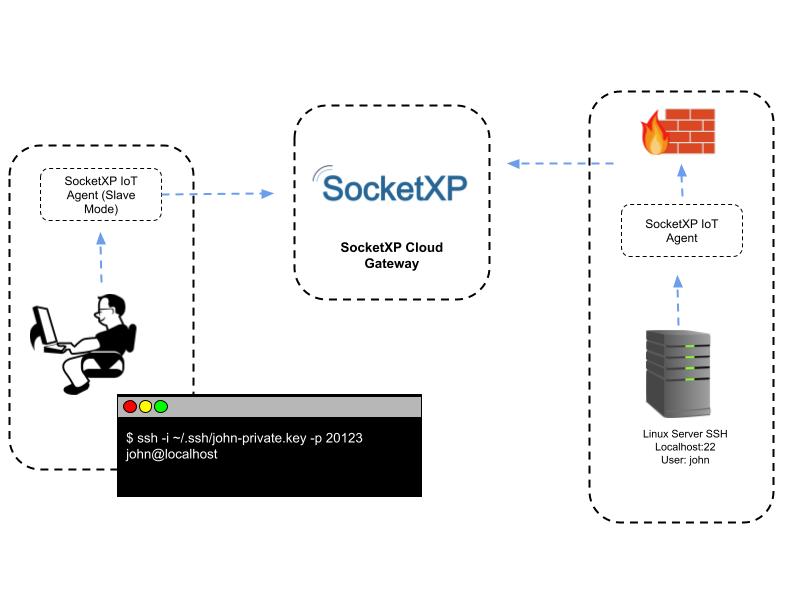
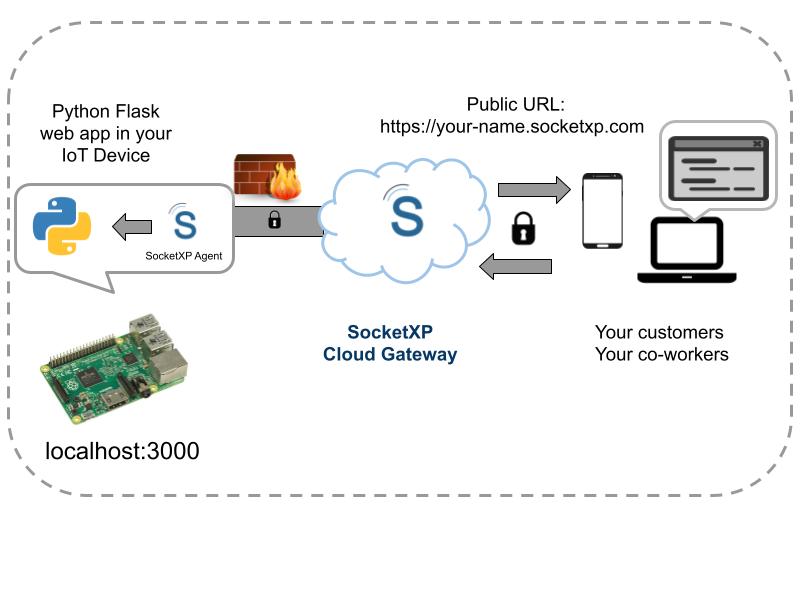
IoT Remote Access SSH Example
Let's explore a practical IoT remote access SSH example. Suppose you have a Raspberry Pi connected to a sensor network, and you need to monitor the sensor data remotely. Here's how you can achieve this using SSH:
- Install SSH Server: On the Raspberry Pi, install the OpenSSH server by running the command
sudo apt-get install openssh-server. - Generate SSH Keys: On your client machine, generate an SSH key pair using the command
ssh-keygen. - Copy Public Key: Copy the public key to the Raspberry Pi using the command
ssh-copy-id pi@raspberrypi.local. - Connect via SSH: From your client machine, connect to the Raspberry Pi using the command
ssh pi@raspberrypi.local.
With this setup, you can securely access the Raspberry Pi and retrieve sensor data without compromising security. This example demonstrates the simplicity and effectiveness of using SSH for IoT remote access.
Best Practices for IoT SSH
To ensure the long-term security and reliability of your IoT SSH setup, follow these best practices:
- Regularly Update Software: Keep the SSH server and client software up to date to protect against known vulnerabilities.
- Monitor Logs: Regularly review SSH logs for suspicious activity and take appropriate action if necessary.
- Limit User Privileges: Restrict SSH access to only those users who require it and limit their privileges to minimize the risk of unauthorized actions.
- Use Two-Factor Authentication: Enhance security by enabling two-factor authentication for SSH connections.
Adhering to these best practices will help you maintain a secure and efficient IoT SSH environment, protecting your devices and data from potential threats.
Troubleshooting SSH Connections
Despite careful setup and configuration, SSH connections can sometimes fail. Below are some common issues and their solutions:
- Connection Refused: Ensure that the SSH service is running and that the firewall allows connections to the SSH port.
- Authentication Failure: Verify that the public key is correctly copied to the server and that the permissions on the authorized_keys file are set correctly.
- Timeout Errors: Check the network connectivity between the client and server, and ensure that the SSH port is not blocked by a router or firewall.
- Permission Denied: Confirm that the user has the necessary permissions to access the server and that the authentication method is correctly configured.
By addressing these issues systematically, you can quickly resolve SSH connection problems and restore secure access to your IoT devices.
Alternative Protocols
While SSH is the most widely used protocol for IoT remote access, other options are available depending on specific requirements. Some alternatives include:
- TLS/SSL: Provides secure communication over HTTP and is often used in web-based IoT applications.
- MQTT: A lightweight messaging protocol suitable for low-bandwidth IoT devices, offering secure communication through SSL/TLS.
- CoAP: Designed for constrained environments, CoAP supports secure communication using DTLS (Datagram Transport Layer Security).
Choosing the right protocol depends on factors such as device capabilities, network conditions, and security requirements. SSH remains a popular choice due to its versatility and strong security features.
Future of IoT and SSH
The future of IoT and SSH is promising, with advancements in technology driving the development of more secure and efficient remote access solutions. As IoT devices continue to evolve, SSH will play a crucial role in ensuring the security and reliability of these systems.
Emerging trends such as quantum-resistant cryptography and AI-driven security measures will further enhance the capabilities of SSH in IoT environments. Developers and administrators must stay informed about these developments to leverage the full potential of SSH for IoT applications.
With the increasing importance of IoT in various industries, the demand for secure and scalable remote access solutions will continue to grow, solidifying SSH's position as a key player in this space.
Conclusion
IoT remote access SSH example provides a secure and reliable method for managing and monitoring IoT devices from remote locations. By understanding the fundamentals of SSH and implementing best practices, you can ensure the security and efficiency of your IoT infrastructure.
We encourage you to explore the examples and guidelines provided in this article and apply them to your own projects. Share your experiences and insights in the comments below, and don't forget to explore other articles on our site for more valuable information on IoT and related technologies.