In the rapidly evolving world of technology, remote SSH IoT over the internet has become a critical tool for managing and securing Internet of Things (IoT) devices from any location. Whether you're a tech enthusiast or a professional, understanding this concept can open doors to endless possibilities in device management and network security.
As IoT devices continue to proliferate across industries, the ability to remotely access and manage them securely is more important than ever. This article will serve as your comprehensive guide to mastering remote SSH IoT over the internet, providing you with the knowledge and tools necessary to implement secure connections for your IoT devices.
Whether you're setting up a smart home, managing industrial automation systems, or developing IoT applications, remote SSH IoT over the internet offers a reliable solution for maintaining control and ensuring data security. Let's dive into the details and explore how you can leverage this powerful technology.
Read also:Hdhub4u Movies
Table of Contents
- Introduction to Remote SSH IoT Over Internet
- Understanding the Basics of SSH
- Overview of IoT and Its Challenges
- Benefits of Using SSH for IoT
- Step-by-Step Guide to Setting Up Remote SSH IoT
- Enhancing Security for Remote SSH IoT
- Tools and Software for Remote SSH IoT
- Real-World Applications of Remote SSH IoT
- Troubleshooting Common Issues
- The Future of Remote SSH IoT Over Internet
- Conclusion and Call to Action
Introduction to Remote SSH IoT Over Internet
Remote SSH IoT over the internet refers to the practice of using Secure Shell (SSH) protocols to remotely access and manage IoT devices connected to the internet. This method ensures secure communication between devices, even when they are geographically distant.
SSH provides encryption and authentication mechanisms that protect data during transmission, making it an ideal solution for IoT applications where security is paramount. Understanding the fundamentals of SSH and its application in IoT is essential for anyone looking to implement remote management solutions.
As we explore this topic further, we will delve into the technical aspects of SSH, its integration with IoT, and the best practices for ensuring secure connections in a connected world.
Understanding the Basics of SSH
What Is SSH?
Secure Shell (SSH) is a cryptographic network protocol designed for secure communication over unsecured networks. It provides a secure channel for accessing remote systems, transferring files, and executing commands. SSH operates on port 22 by default and supports various encryption algorithms to ensure data privacy.
Key features of SSH include:
- Encryption of data during transmission
- Authentication mechanisms to verify user identity
- Support for secure file transfers through SFTP
Why Use SSH for IoT?
IoT devices often lack robust security features, making them vulnerable to cyberattacks. SSH addresses these vulnerabilities by providing a secure method for accessing and managing devices remotely. Its encryption capabilities ensure that sensitive data remains protected, even when transmitted over public networks.
Read also:7movierulz 7movierulz
Additionally, SSH supports public key authentication, which eliminates the need for passwords and reduces the risk of unauthorized access.
Overview of IoT and Its Challenges
The Internet of Things (IoT) encompasses a vast network of interconnected devices that communicate and exchange data over the internet. While IoT has revolutionized industries and improved efficiency, it also presents unique challenges, particularly in terms of security and scalability.
One of the primary concerns with IoT devices is their susceptibility to cyber threats. Many devices lack adequate security measures, making them easy targets for hackers. Remote SSH IoT over the internet addresses these concerns by providing a secure and reliable method for managing devices.
Other challenges include:
- Device heterogeneity
- Scalability issues
- Data privacy concerns
Benefits of Using SSH for IoT
Enhanced Security
SSH offers robust encryption and authentication mechanisms that protect IoT devices from unauthorized access. Its ability to secure data during transmission ensures that sensitive information remains confidential and intact.
Reliability and Performance
SSH connections are reliable and efficient, making them ideal for managing IoT devices in real-time. The protocol supports various compression algorithms, which reduce bandwidth usage and improve performance.
Scalability
SSH can be easily scaled to accommodate large numbers of IoT devices, making it a practical solution for enterprise-level deployments. Its support for automation and scripting further enhances its scalability and usability.
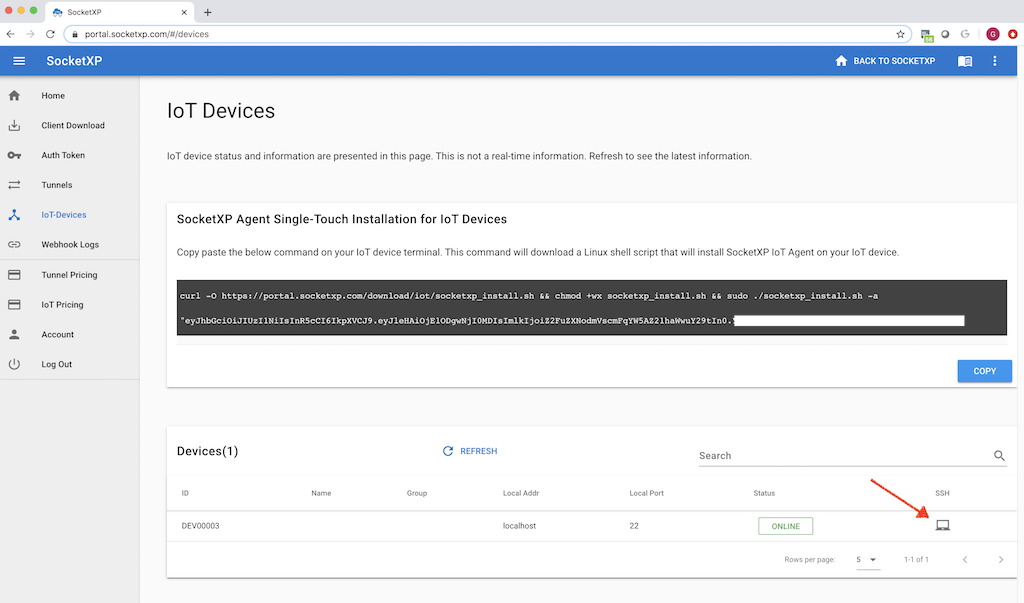
Step-by-Step Guide to Setting Up Remote SSH IoT
1. Install SSH Server on IoT Device
The first step in setting up remote SSH IoT over the internet is to install an SSH server on your IoT device. Most Linux-based devices come with SSH pre-installed, but if not, you can install it using package managers like apt or yum.
2. Configure Firewall Settings
Ensure that your firewall allows incoming connections on port 22 (or a custom port if you choose to change it). This step is crucial for enabling remote access to your IoT device.
3. Set Up Public Key Authentication
Public key authentication eliminates the need for passwords, enhancing security and convenience. Generate a key pair on your local machine and copy the public key to the IoT device's authorized_keys file.
4. Test the Connection
Once everything is configured, test the connection by initiating an SSH session from your local machine to the IoT device. Verify that you can access the device securely without entering a password.
Enhancing Security for Remote SSH IoT
Change Default SSH Port
Changing the default SSH port from 22 to a non-standard port reduces the risk of brute-force attacks. This simple measure can significantly improve the security of your IoT devices.
Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide two forms of identification before gaining access. This can be implemented using tools like Google Authenticator or hardware tokens.
Regularly Update Firmware
Keeping your IoT device's firmware up to date ensures that you have the latest security patches and features. Regular updates help protect your devices from known vulnerabilities.
Tools and Software for Remote SSH IoT
Several tools and software solutions are available to simplify the process of managing remote SSH IoT connections. Some popular options include:
- Putty: A widely used SSH client for Windows
- OpenSSH: A free and open-source SSH suite for Linux and Unix-based systems
- Bitvise: A feature-rich SSH client and server for Windows
These tools provide a user-friendly interface and advanced features to enhance your remote SSH IoT experience.
Real-World Applications of Remote SSH IoT
Smart Home Automation
Remote SSH IoT enables homeowners to manage their smart home devices from anywhere in the world. This includes controlling lighting, thermostats, security systems, and more.
Industrial Automation
In industrial settings, remote SSH IoT allows engineers to monitor and control machinery and processes in real-time, improving efficiency and reducing downtime.
Healthcare
IoT devices in healthcare, such as wearable health monitors and remote patient monitoring systems, benefit from secure SSH connections to ensure patient data privacy and security.
Troubleshooting Common Issues
While setting up remote SSH IoT over the internet, you may encounter various issues. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH server is running and that firewall rules allow incoming connections.
- Authentication Failed: Verify that your public key is correctly added to the authorized_keys file on the IoT device.
- Slow Connection: Optimize your SSH configuration by enabling compression and limiting bandwidth usage.
The Future of Remote SSH IoT Over Internet
As IoT continues to evolve, the role of remote SSH IoT over the internet will become increasingly significant. Advances in encryption technologies, quantum computing, and AI-driven security solutions will further enhance the capabilities of SSH, making it an even more powerful tool for managing IoT devices.
In the coming years, we can expect to see more integrated solutions that combine SSH with other protocols and technologies to create seamless and secure IoT ecosystems.
Conclusion and Call to Action
Remote SSH IoT over the internet is a vital technology for managing and securing IoT devices in today's interconnected world. By understanding its fundamentals and implementing best practices, you can ensure that your devices remain protected and operational from anywhere in the world.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles on IoT and cybersecurity to deepen your knowledge and stay ahead of the curve. Together, let's build a safer and more connected future!