IoT remote access behind router is a crucial concept in the modern era of connected devices. As more devices integrate into the Internet of Things (IoT) ecosystem, understanding how to securely and efficiently access these devices remotely has become essential for both individuals and businesses. Whether you're a tech enthusiast, a network administrator, or simply someone interested in smart home solutions, this guide will provide you with the knowledge you need to navigate the complexities of IoT remote access.
In recent years, IoT devices have revolutionized the way we interact with technology. From smart thermostats and security cameras to industrial sensors and healthcare devices, IoT has enabled us to monitor and control our environment like never before. However, accessing these devices remotely, especially when they are behind a router, presents unique challenges that must be addressed to ensure security and functionality.
This article delves deep into the world of IoT remote access, exploring the technologies, methods, and best practices involved. By the end of this guide, you'll have a comprehensive understanding of how to set up, secure, and troubleshoot IoT remote access behind a router, empowering you to take full advantage of your connected devices.
Read also:Movieruz
Table of Contents
- Introduction to IoT Remote Access
- Understanding IoT Network Architecture
- Methods for IoT Remote Access
- Security Considerations for IoT Remote Access
- Tools and Technologies for IoT Remote Access
- Troubleshooting IoT Remote Access Issues
- Best Practices for IoT Remote Access
- Applications of IoT Remote Access
- The Future of IoT Remote Access
- Conclusion
Introduction to IoT Remote Access
IoT remote access behind router refers to the ability to access IoT devices located within a private network from an external location. This capability is vital for managing and monitoring devices in various settings, such as smart homes, industrial facilities, and healthcare environments.
Remote access allows users to control devices, retrieve data, and perform maintenance without physical presence. However, achieving secure and reliable remote access requires a thorough understanding of networking principles, security protocols, and available technologies.
Some of the key benefits of IoT remote access include increased efficiency, cost savings, and enhanced convenience. For instance, businesses can monitor and manage their IoT infrastructure from anywhere, reducing the need for on-site visits. Similarly, individuals can control their smart home devices while on vacation or at work, ensuring security and comfort.
Understanding IoT Network Architecture
Basic Components of IoT Networks
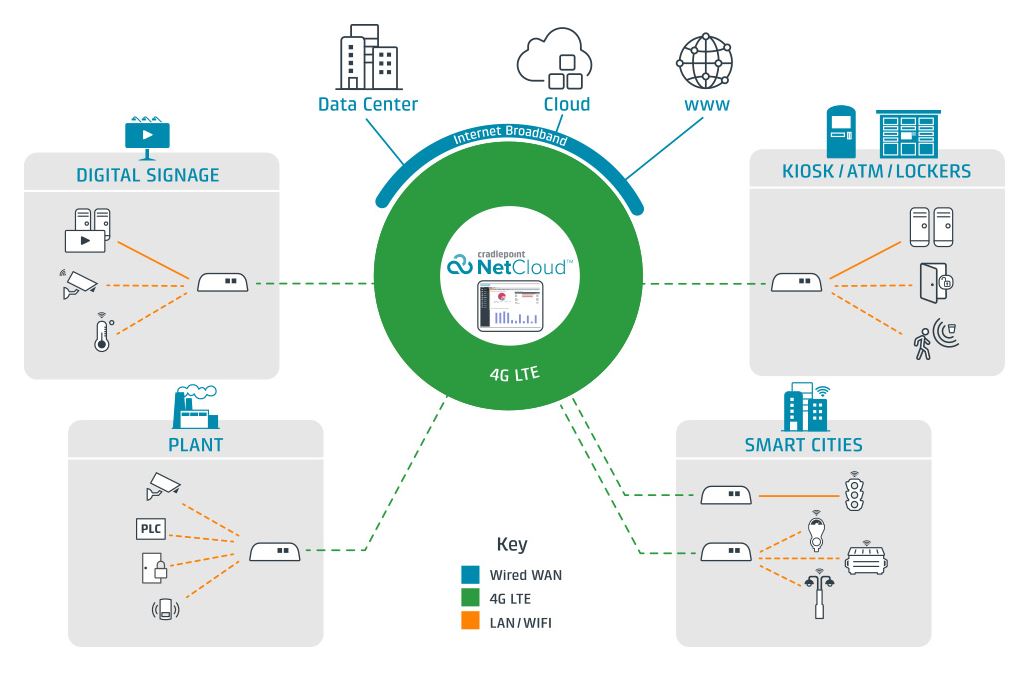
To grasp IoT remote access behind router, it's essential to understand the architecture of IoT networks. These networks typically consist of the following components:
- Devices: Sensors, actuators, and other IoT devices that collect and transmit data.
- Gateway: A device that connects IoT devices to the internet or a local network.
- Router: A networking device that directs traffic between the local network and the internet.
- Cloud Platform: A centralized system where data is processed, stored, and analyzed.
Network Topologies
IoT networks can be structured in various topologies, each with its own advantages and limitations:
- Star Topology: Devices connect directly to a central hub or gateway.
- Mesh Topology: Devices communicate with each other directly, forming a resilient network.
- Hybrid Topology: Combines elements of star and mesh topologies for optimal performance.
Methods for IoT Remote Access
Port Forwarding
Port forwarding is a common method for enabling IoT remote access behind router. By configuring the router to forward specific ports to the IoT device, users can access the device from an external network. However, this approach requires careful configuration and poses potential security risks if not implemented correctly.
Read also:Www Tamilblasters Com 2024
Virtual Private Networks (VPNs)
VPNs provide a secure tunnel for remote access, encrypting data transmitted between the user and the IoT device. This method is particularly useful for protecting sensitive information and ensuring privacy.
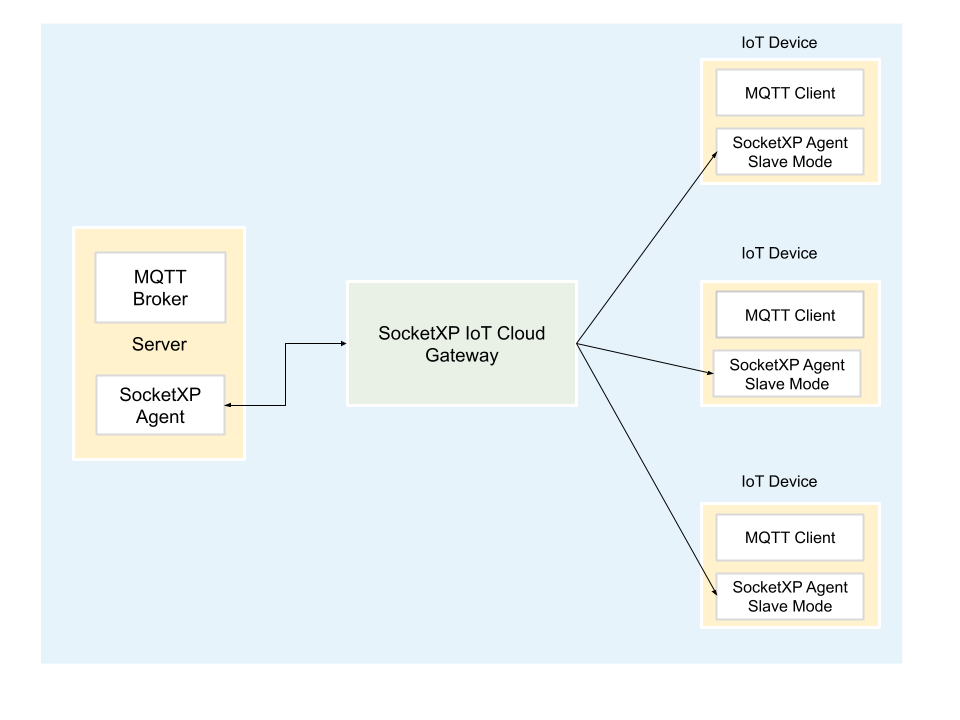
Cloud-Based Solutions
Many IoT platforms offer cloud-based solutions that simplify remote access. These platforms handle the complexities of networking and security, allowing users to focus on managing their devices.
Security Considerations for IoT Remote Access
Authentication and Authorization
Implementing robust authentication and authorization mechanisms is critical for securing IoT remote access. Multi-factor authentication (MFA) and role-based access control (RBAC) are effective strategies for ensuring only authorized users can access IoT devices.
Data Encryption
Encrypting data transmitted between the user and the IoT device is essential for protecting sensitive information. Protocols such as TLS (Transport Layer Security) and HTTPS should be used whenever possible.
Regular Updates and Patching
Keeping IoT devices and associated software up to date is vital for addressing vulnerabilities and ensuring security. Manufacturers and developers should provide regular updates and patches to fix any identified issues.
Tools and Technologies for IoT Remote Access
Popular IoT Platforms
Several platforms cater specifically to IoT remote access, offering a range of features and functionalities. Some of the most popular platforms include:
- Amazon Web Services (AWS) IoT
- Microsoft Azure IoT
- Google Cloud IoT
Software Tools
Various software tools can facilitate IoT remote access, such as:
- TeamViewer
- AnyDesk
- Putty
Troubleshooting IoT Remote Access Issues
Common Problems
When setting up IoT remote access behind router, users may encounter several common issues:
- Connection Errors: Caused by misconfigured settings or network issues.
- Security Alerts: Triggered by unauthorized access attempts or outdated software.
- Performance Degradation: Resulting from insufficient bandwidth or high latency.
Solutions
To resolve these issues, users can:
- Verify router settings and port configurations.
- Update firmware and software to the latest versions.
- Optimize network performance by reducing unnecessary traffic.
Best Practices for IoT Remote Access
Adhering to best practices is crucial for ensuring secure and reliable IoT remote access:
- Use strong, unique passwords for all devices and accounts.
- Regularly monitor network activity for suspicious behavior.
- Implement network segmentation to isolate IoT devices from other systems.
Applications of IoT Remote Access
Smart Homes
IoT remote access enables homeowners to control lighting, climate, and security systems from anywhere, enhancing convenience and safety.
Industrial Automation
In industrial settings, remote access allows engineers to monitor and manage equipment, reducing downtime and improving efficiency.
Healthcare
Healthcare providers can use IoT remote access to monitor patients' vital signs and adjust treatment plans in real time.
The Future of IoT Remote Access
As IoT technology continues to evolve, so too will the methods and tools for remote access. Emerging trends such as 5G connectivity, edge computing, and artificial intelligence (AI) will play a significant role in shaping the future of IoT remote access.
These advancements promise to enhance performance, security, and scalability, making IoT remote access even more accessible and reliable for users worldwide.
Conclusion
In conclusion, IoT remote access behind router is a vital capability for managing and monitoring connected devices in today's digital landscape. By understanding the architecture, methods, and security considerations involved, users can take full advantage of their IoT infrastructure while ensuring safety and privacy.
We encourage you to apply the knowledge gained from this guide to enhance your IoT setup. Feel free to leave a comment or share this article with others who may find it useful. For more insights into IoT and related technologies, explore our other articles on the site.