In today's digital landscape, remote IoT firewall examples play a vital role in securing connected devices and networks. As more devices join the Internet of Things (IoT), the need for robust security measures becomes increasingly important. RemoteIoT firewalls are designed to protect devices, networks, and data from unauthorized access and cyber threats.
With the rapid expansion of IoT technology, organizations and individuals face growing security challenges. Cybercriminals are constantly searching for vulnerabilities in connected systems, making it essential to implement effective security solutions. RemoteIoT firewalls provide a layer of protection that helps mitigate risks and ensures the safety of sensitive information.
In this article, we'll explore various remote IoT firewall examples, their functionalities, and how they contribute to network security. By understanding the importance of these tools, you can better protect your devices and networks from potential threats.
Read also:Ullu Web Series Download Tamil
Table of Contents
- Introduction to RemoteIoT Firewall
- Importance of RemoteIoT Firewall
- Types of Firewalls for RemoteIoT
- Examples of RemoteIoT Firewalls
- Configuring RemoteIoT Firewall
- Best Practices for RemoteIoT Firewall
- Challenges in Implementing RemoteIoT Firewall
- Future of RemoteIoT Firewall
- Conclusion
- Frequently Asked Questions
Introduction to RemoteIoT Firewall
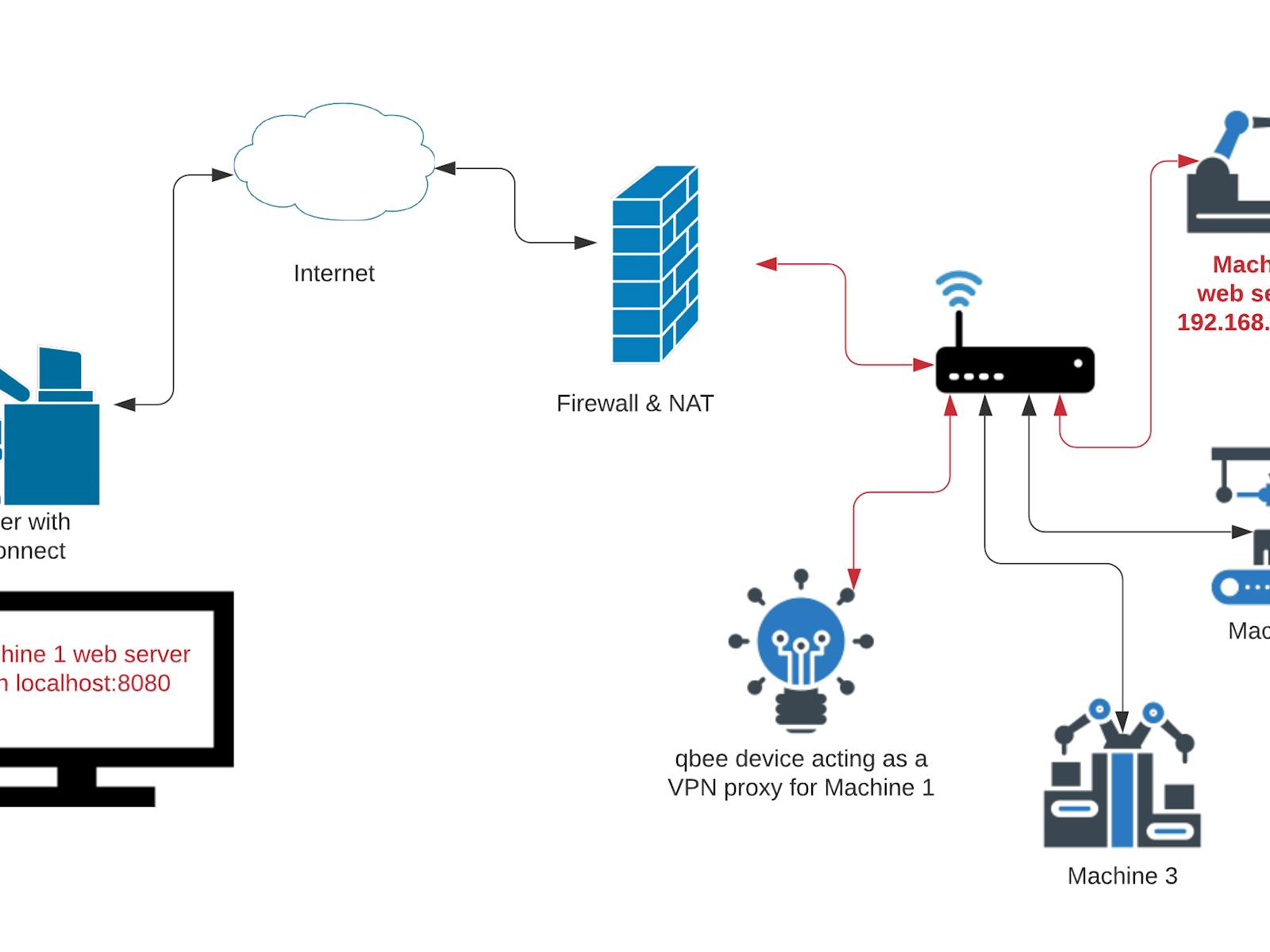
A remote IoT firewall is a security solution specifically designed to protect Internet of Things devices and networks from unauthorized access, malicious attacks, and other cyber threats. These firewalls can be deployed in various environments, including home networks, small businesses, and large enterprises.
RemoteIoT firewalls operate by filtering incoming and outgoing traffic based on predefined rules and policies. This ensures that only legitimate traffic is allowed to pass through while blocking potentially harmful activity. Additionally, these firewalls often include advanced features such as intrusion detection, deep packet inspection, and real-time threat monitoring.
As IoT adoption continues to grow, the demand for reliable and efficient remote IoT firewall solutions is expected to increase. By understanding the different types of firewalls and their capabilities, organizations can better protect their networks and devices from potential threats.
Importance of RemoteIoT Firewall
RemoteIoT firewalls are crucial for safeguarding connected devices and networks against cyber threats. With the increasing number of IoT devices being deployed globally, the risk of cyberattacks has grown exponentially. According to a report by Cybersecurity Ventures, cybercrime damages are projected to reach $10.5 trillion annually by 2025.
Implementing a remote IoT firewall provides several benefits, including:
- Enhanced network security
- Protection against unauthorized access
- Real-time threat detection and mitigation
- Improved compliance with industry regulations
By investing in a robust remote IoT firewall solution, organizations can significantly reduce the risk of data breaches and other security incidents.
Read also:Movieruz
Types of Firewalls for RemoteIoT
There are several types of firewalls available for remote IoT environments. Each type offers unique features and capabilities that cater to specific security needs. Below are some of the most common types of firewalls used in remote IoT networks:
Packet Filtering Firewalls
Packet filtering firewalls analyze individual packets of data as they pass through the network. These firewalls allow or deny traffic based on predefined rules, such as IP addresses, port numbers, and protocols. While simple and efficient, packet filtering firewalls lack the ability to inspect the content of packets, making them less effective against sophisticated attacks.
Stateful Inspection Firewalls
Stateful inspection firewalls monitor the state of active connections and use this information to make more informed decisions about allowing or denying traffic. This type of firewall provides better security than packet filtering firewalls by considering the context of each connection.
Application-Level Firewalls
Application-level firewalls inspect traffic at the application layer, allowing for more granular control over which applications and services are permitted. These firewalls can detect and block malicious activity that may bypass other types of firewalls.
Examples of RemoteIoT Firewalls
Here are some examples of remote IoT firewalls that are widely used in various industries:
Example 1: pfSense
pfSense is an open-source firewall and router platform based on FreeBSD. It offers a wide range of features, including stateful packet filtering, NAT, and VLAN support. pfSense is highly customizable and can be tailored to meet the specific needs of remote IoT environments.
Example 2: OPNsense
OPNsense is another open-source firewall solution that provides robust security features for remote IoT networks. It includes intrusion detection and prevention, load balancing, and advanced routing capabilities. OPNsense is known for its ease of use and frequent updates, ensuring that users have access to the latest security patches.
Example 3: Sophos XG Firewall
Sophos XG Firewall is a commercial firewall solution that offers comprehensive protection for remote IoT networks. It includes features such as web filtering, antivirus, and sandboxing to detect and block advanced threats. Sophos XG Firewall is designed to be scalable, making it suitable for organizations of all sizes.
Configuring RemoteIoT Firewall
Configuring a remote IoT firewall involves several steps to ensure optimal performance and security. Below are some key considerations when setting up a remote IoT firewall:
- Define clear security policies and rules
- Regularly update firmware and software
- Monitor network activity for suspicious behavior
- Implement multi-factor authentication for remote access
By following these best practices, organizations can maximize the effectiveness of their remote IoT firewall and reduce the risk of security breaches.
Best Practices for RemoteIoT Firewall
To ensure the best possible protection for your remote IoT network, consider implementing the following best practices:
- Use strong passwords and encryption for all devices and connections
- Segment your network to isolate sensitive devices and data
- Regularly review and update firewall rules to adapt to new threats
- Perform routine audits to identify and address vulnerabilities
By adhering to these guidelines, you can enhance the security of your remote IoT network and protect against potential threats.
Challenges in Implementing RemoteIoT Firewall
While remote IoT firewalls offer numerous benefits, there are also challenges associated with their implementation. Some common challenges include:
- Complexity in configuring and managing firewall rules
- Resource constraints, such as limited bandwidth and processing power
- Keeping up with the rapidly evolving threat landscape
To overcome these challenges, organizations should invest in proper training and support for their IT teams. Additionally, leveraging automated tools and services can help streamline the management of remote IoT firewalls.
Future of RemoteIoT Firewall
As IoT technology continues to evolve, so too will the role of remote IoT firewalls in securing connected devices and networks. Emerging trends such as artificial intelligence, machine learning, and cloud-based solutions are expected to play a significant role in shaping the future of remote IoT firewalls.
These advancements will enable firewalls to become more intelligent and adaptive, capable of detecting and responding to threats in real-time. Furthermore, the integration of remote IoT firewalls with other security solutions, such as endpoint protection and threat intelligence platforms, will provide a more holistic approach to network security.
Conclusion
RemoteIoT firewall examples are essential tools for protecting connected devices and networks from cyber threats. By understanding the different types of firewalls and their capabilities, organizations can better secure their IoT environments and reduce the risk of security incidents.
We encourage you to explore the various remote IoT firewall solutions available and determine which one best suits your needs. Additionally, don't forget to implement best practices and stay informed about the latest trends and developments in the field of network security.
Feel free to leave a comment or question below, and share this article with others who may benefit from the information provided.
Frequently Asked Questions
What is a remote IoT firewall?
A remote IoT firewall is a security solution designed to protect Internet of Things devices and networks from unauthorized access and cyber threats.
Why are remote IoT firewalls important?
Remote IoT firewalls are crucial for safeguarding connected devices and networks against cyber threats, ensuring the security and integrity of sensitive data.
What are some examples of remote IoT firewalls?
Some examples of remote IoT firewalls include pfSense, OPNsense, and Sophos XG Firewall.
How can I configure a remote IoT firewall?
To configure a remote IoT firewall, define clear security policies and rules, regularly update firmware and software, monitor network activity, and implement multi-factor authentication for remote access.