In today's digital landscape, web-based SSH solutions have become an essential tool for businesses and individuals seeking secure remote access to servers and networks. As more organizations transition to remote work models, the demand for reliable and efficient web-based SSH solutions continues to grow. These tools provide users with seamless access to their systems without the need for complex installations or configurations.
With the rise of cyber threats and data breaches, ensuring secure communication between devices has never been more critical. Web-based SSH solutions offer encrypted connections that protect sensitive information from unauthorized access. Whether you're managing a small startup or overseeing a large enterprise, understanding how these solutions work can significantly enhance your cybersecurity posture.
This comprehensive guide will explore everything you need to know about web-based SSH solutions, including their benefits, implementation strategies, best practices, and potential challenges. By the end of this article, you'll have a clear understanding of why these tools are vital for modern businesses and how to choose the right solution for your needs.
Read also:5movierulz 2022 Download
Table of Contents
- Introduction to Web-Based SSH
- Benefits of Web-Based SSH Solutions
- How Web-Based SSH Works
- Types of Web-Based SSH Solutions
- Choosing the Right Web-Based SSH Solution
- Implementation Strategies for Web-Based SSH
- Best Practices for Using Web-Based SSH
- Common Challenges and Solutions
- Security Considerations for Web-Based SSH
- The Future of Web-Based SSH Solutions
Introduction to Web-Based SSH
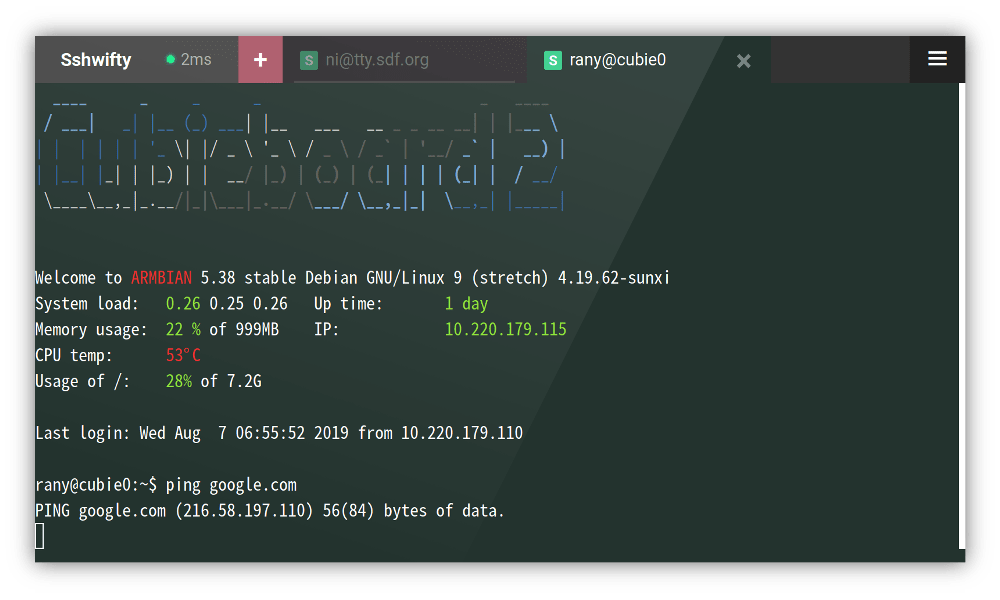
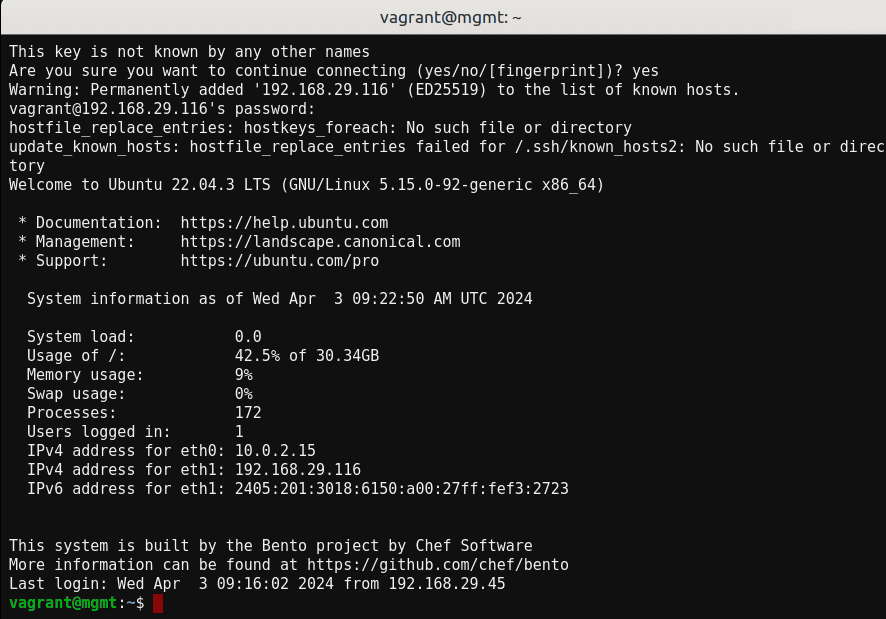
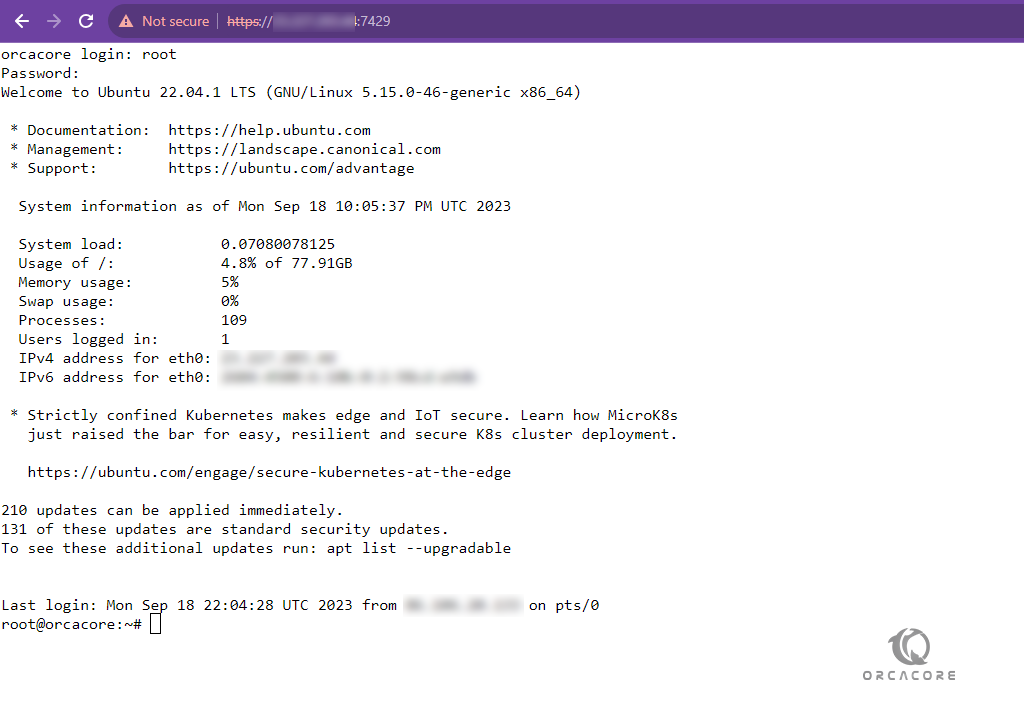
Web-based SSH (Secure Shell) solutions enable users to access remote servers through a web browser without requiring a dedicated SSH client. This technology simplifies the process of managing servers by providing a user-friendly interface that eliminates the need for complex configurations.
What Is SSH?
SSH is a cryptographic network protocol designed to secure communication between devices over an unsecured network. It provides encrypted data transfer, authentication mechanisms, and integrity checks to protect against unauthorized access and data tampering.
Why Use Web-Based SSH?
Web-based SSH solutions offer several advantages over traditional SSH clients, including:
- Platform independence: Users can access servers from any device with a web browser.
- Easy deployment: No need to install additional software on client machines.
- Centralized management: Administrators can manage multiple servers from a single interface.
Benefits of Web-Based SSH Solutions
Adopting web-based SSH solutions can bring numerous benefits to organizations of all sizes. These tools not only enhance security but also improve efficiency and productivity.
Enhanced Security
Web-based SSH solutions provide robust encryption and authentication mechanisms, ensuring that sensitive information remains protected during transmission. This is particularly important for businesses handling confidential data such as financial records or personal identifiable information (PII).
Improved Accessibility
With web-based SSH, users can access servers from anywhere in the world using any device with an internet connection. This flexibility is especially valuable for remote teams who need to collaborate on projects without being physically present in the office.
Read also:Movierlz
Cost-Effective
Eliminating the need for dedicated SSH clients reduces costs associated with software licenses and maintenance. Additionally, centralized management simplifies administrative tasks, freeing up IT resources for other critical activities.
How Web-Based SSH Works
Web-based SSH solutions function by establishing a secure connection between a client's web browser and a remote server. This process involves several steps:
- The user accesses the web-based SSH interface through a URL provided by the administrator.
- Authentication occurs using credentials such as username and password, or more advanced methods like multi-factor authentication (MFA).
- Once authenticated, the user gains access to the server's command-line interface within their browser.
- Data transmitted between the browser and server is encrypted to prevent interception by malicious actors.
Types of Web-Based SSH Solutions
There are various types of web-based SSH solutions available in the market, each catering to different needs and preferences:
Open-Source Solutions
Open-source web-based SSH tools allow users to customize and extend functionality according to their requirements. Examples include ShellInABox and Ajaxterm.
Commercial Solutions
Commercial offerings often come with additional features such as advanced security controls, monitoring capabilities, and technical support. Popular options include CloudShell and SecureLink.
Cloud-Based Solutions
Cloud-based web-based SSH services provide scalability and flexibility, making them ideal for organizations with dynamic workloads. These solutions typically operate on a subscription model, allowing businesses to pay only for what they use.
Choosing the Right Web-Based SSH Solution
Selecting the appropriate web-based SSH solution depends on several factors, including:
- Size and complexity of your infrastructure
- Security requirements
- Budget constraints
- Technical expertise of your team
- Integration capabilities with existing systems
Conducting a thorough evaluation of available options and consulting with industry experts can help ensure you choose the best solution for your organization.
Implementation Strategies for Web-Based SSH
Successfully deploying web-based SSH solutions requires careful planning and execution. Consider the following strategies:
Plan Your Deployment
Define objectives, identify stakeholders, and establish timelines to ensure a smooth implementation process.
Test Thoroughly
Before rolling out the solution enterprise-wide, test it in a controlled environment to identify potential issues and refine configurations.
Train Your Team
Provide comprehensive training to all users and administrators to maximize the benefits of the new system.
Best Practices for Using Web-Based SSH
To get the most out of your web-based SSH solution, follow these best practices:
- Enable strong authentication methods such as MFA.
- Regularly update software to patch vulnerabilities.
- Monitor activity logs for suspicious behavior.
- Restrict access based on user roles and responsibilities.
Common Challenges and Solutions
While web-based SSH solutions offer many advantages, they also present certain challenges. Addressing these issues proactively can prevent disruptions and enhance overall performance.
Performance Issues
Optimize server resources and network configurations to ensure smooth operation under heavy loads.
Security Concerns
Implement robust security measures, including encryption, firewalls, and intrusion detection systems, to safeguard against potential threats.
Security Considerations for Web-Based SSH
Security should always be a top priority when implementing web-based SSH solutions. Consider the following:
- Use strong, unique passwords and enable password expiration policies.
- Limit access to trusted IP addresses whenever possible.
- Regularly review and update security policies to address emerging threats.
The Future of Web-Based SSH Solutions
As technology continues to evolve, so too will web-based SSH solutions. Advances in areas such as artificial intelligence, machine learning, and quantum computing are likely to influence future developments, offering even greater capabilities and security enhancements.
Conclusion
Web-based SSH solutions represent a powerful tool for securing remote access to servers and networks. By understanding their benefits, implementation strategies, and best practices, organizations can harness these technologies to improve security, efficiency, and productivity.
We encourage readers to share their experiences with web-based SSH solutions in the comments section below. Additionally, feel free to explore other articles on our site for more insights into cybersecurity and IT management.
Data sources: National Institute of Standards and Technology (NIST), Cybersecurity and Infrastructure Security Agency (CISA), and Open Web Application Security Project (OWASP).